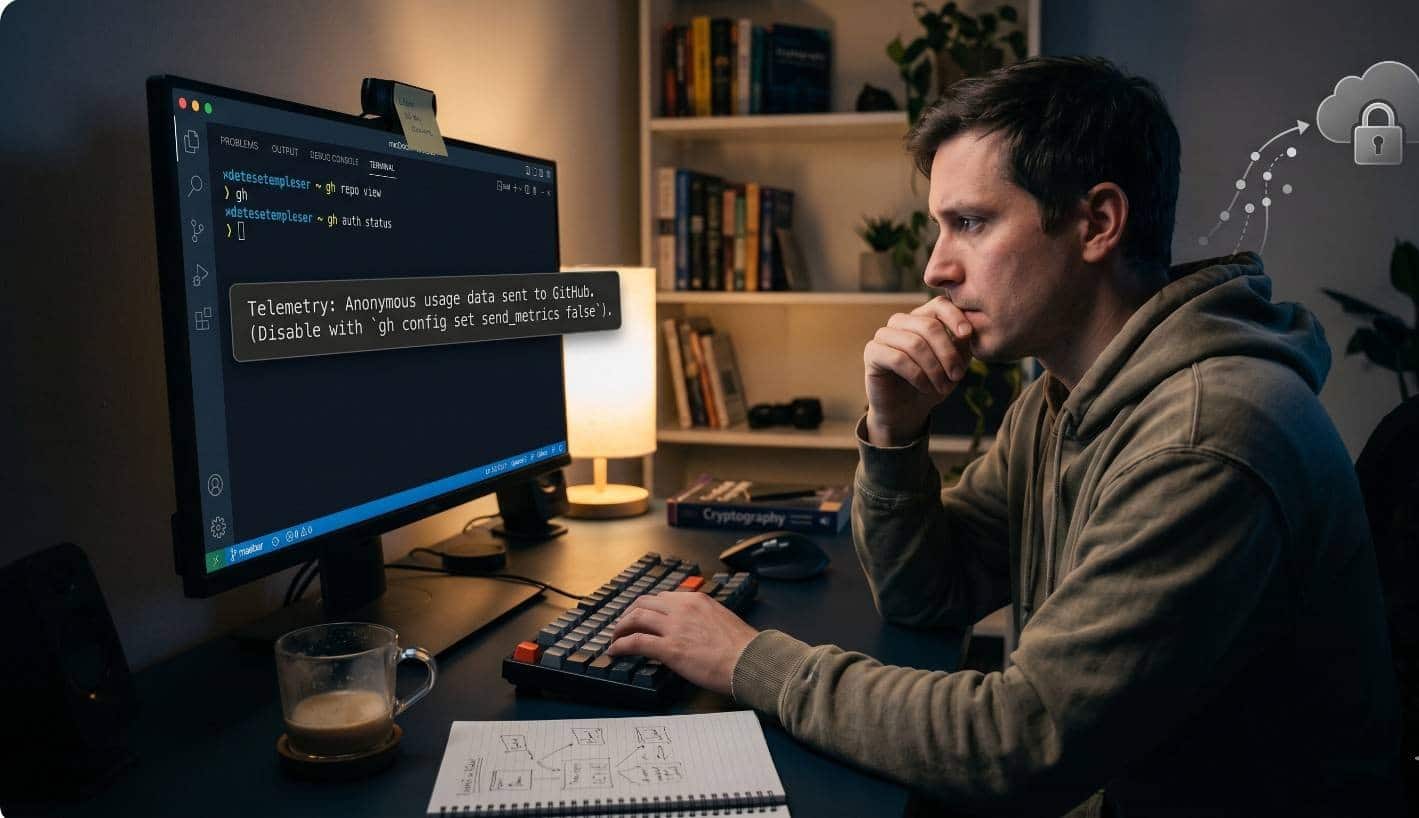
In the today’s software landscape, the tools we use are no longer static binaries living in isolation on our hard drives. They are living, breathing entities that communicate constantly with the mothership. Among these, the GitHub Command Line Interface (CLI), known simply as “gh,” has become a staple for developers looking to bridge the gap between their local terminal and the cloud-hosted repositories they manage. However, beneath the surface of streamlined pull requests and issue tracking lies a silent conversation: telemetry.
The decision by GitHub to implement pseudoanonymous telemetry has sparked a quiet but persistent firestorm within the open-source community. It raises a fundamental question: when does a tool stop serving the developer and start serving the corporation? For those providing Website Maintenance and support Services, the integrity of the development environment is not just a matter of preference it is a matter of professional liability and client trust.
What is the “Pseudo” in Pseudoanonymous
To the average user, “anonymous” sounds safe. It implies that their identity is scrubbed from the record. But GitHub uses the term “pseudoanonymous,” a linguistic middle ground that carries significant weight. In the context of the GitHub CLI, this means that while your name, email address, and specific repository secrets aren’t being sent in a raw text format, your actions are linked to a unique identifier.
This identifier acts as a digital fingerprint. It allows GitHub to see that a single user performed a sequence of actions perhaps checking out a branch, running a test, and then pushing a commit without explicitly knowing the username. However, the risk of “re-identification” is the elephant in the room. When a tool knows exactly what time a command was run, what version of the operating system was used, and the unique ID of the machine, it doesn’t take much to cross-reference that data with public GitHub logs to figure out exactly who was behind the keyboard.
The Opt-Out Culture vs. Privacy by Design
One of the most contentious aspects of this telemetry implementation is its “opt-out” nature. When you install the GitHub CLI, the tracking is turned on by default. This flips the script on traditional privacy ethics, which suggest that tracking should be an “opt-in” choice made by an informed user.
By forcing users to proactively hunt down the command to disable tracking using “gh config set telemetry off” GitHub relies on “choice architecture” to maximize data collection. Most developers are busy. They are debugging complex issues, meeting deadlines, and managing workflows. They often don’t have the time to read through the fine print of every update. This inertia is a powerful tool for data harvesting.
The Ethical Dilemma of Productivity
GitHub’s justification for this collection is centered on product improvement. They argue that by seeing which commands fail and which are most popular, they can build a better tool. From a product management perspective, this is gold. It removes the guesswork from the development cycle. If they see that a large percentage of users struggle with the syntax of a specific flag, they can simplify it in the next release.
However, this “productivity” comes at the cost of the developer’s mental model of their machine. For decades, the terminal was seen as a private sanctuary. It was the one place where a developer could work without being watched. The introduction of telemetry into core CLI tools shatters this illusion of privacy. It introduces a “Panopticon effect” where the developer, knowing they are being observed, might change their behavior or feel a sense of unease in their own workspace.
Impact on Professional Services
For agencies and freelancers, this is more than just a philosophical debate. When you are hired to handle Website Maintenance and support Services, you are often working on proprietary codebases for clients who have strict non-disclosure agreements. While GitHub claims they don’t collect “sensitive arguments,” the definition of sensitivity can be blurry.
If a CLI tool leaks metadata about a private project’s structure or the frequency of its updates, it could theoretically give competitors insights into a company’s release cycle or internal technical hurdles. As a result, many high-security environments now mandate the total disabling of telemetry across all developer machines as a standard security protocol. When maintaining a client’s site, the last thing a professional wants is for their local toolchain to be a source of data leakage.
Technical Leakage: What’s Really Going Over the Wire?
When we look at the data payloads sent by the GitHub CLI, we see things like the command name, the time taken to execute, and the “exit code.” On the surface, this seems harmless. But metadata is often more revealing than data itself. A high frequency of “exit code 1” (failure) on a specific security-related command could indicate a developer struggling with a vulnerability, or perhaps an automated system being targeted by an attack.

Furthermore, the environment variables of a machine often sent as part of telemetry to help developers debug “platform-specific” issues can reveal a lot about a user’s local network, other installed software, and even their physical location via IP address. The cumulative effect of these small data points creates a profile that is far from truly anonymous.
The Slippery Slope of Default On
The GitHub CLI is just one example. We are seeing a trend where developer tools from code editors to package managers and cloud CLIs are all moving toward a “telemetry-first” mindset. If the community doesn’t push back against the GitHub CLI’s implementation, it sets a precedent that the terminal is no longer a private space. It signals to other toolmakers that developers are willing to trade their privacy for minor feature improvements.
For a community built on the principles of open source and transparency, this move feels like a step backward. Developers value the ability to audit their code and their tools. When a tool hides its data collection behind a “pseudoanonymous” label and enables it by default, it erodes the trust that the open-source movement has spent decades building.
Practical Steps for the Privacy-Conscious
If you are concerned about this trend, there are several steps you can take to harden your environment:
- Hard-set your environment: Don’t just rely on the CLI config. Add “export GH_NO_TELEMETRY=1” to your shell profile (like .bashrc or .zshrc). This ensures that even if you reset your config or update the tool, the tracking remains off.
- Audit your tools: Periodically check which of your installed CLI tools are making network requests. You can use network monitoring tools to alert you when a local command tries to communicate with an external server.
- Educate your team: If you are managing a team or providing Website Maintenance and support Services, make privacy settings part of your “onboarding” script. Ensure that every developer starts with a clean, private environment that doesn’t leak data back to third-party vendors.
Conclusion: A Call for Transparency
The GitHub CLI is a remarkable tool that has undoubtedly made the lives of developers easier. But ease of use should not come at the expense of fundamental privacy. “Pseudoanonymous” is a clever marketing term that masks a deeper intrusion into the developer’s workflow.
We need to demand “Privacy by Design.” Telemetry should be a conversation, not a hidden default. It should be an invitation to help improve the tool, offered to the user upon the first run, rather than a background process that requires a manual search to disable. Until the industry shifts back to an “opt-in” model, the burden remains on the developer to lock the door and close the curtains of their digital workshop. Keeping a development environment clean and private is now a core part of professional digital hygiene.
Frequently Asked Questions
What exactly is “pseudoanonymous” telemetry?
Pseudoanonymous telemetry is a method of data collection where direct identifiers like your name or email are removed and replaced with a unique, randomized ID. While this makes it harder to immediately identify you, the data is not truly anonymous because the unique ID allows a company to track a single user’s behavior over time. If this ID is cross-referenced with other public data, it is often possible to link the actions back to a specific individual.
Is the GitHub CLI stealing my code?
No. According to GitHub’s official documentation, the CLI does not collect “sensitive” information. This means it is designed to ignore the specific arguments you type (like passwords, commit messages, or filenames) and only record the core commands you use, such as gh pr create or gh issue list. However, the fact that it tracks when and how you use these commands is what raises privacy concerns.
Why is telemetry enabled by default?
GitHub, like many modern software companies, uses an “opt-out” model because it ensures they get a much larger dataset. Most users never change default settings. GitHub argues that this data is essential for identifying bugs, understanding which features are most popular, and deciding which parts of the tool need more development focus.
Can I see what data is being sent before I disable it?
Yes. If you want to audit the data yourself, you can run the command with a specific prefix: GH_LOG_TELEMETRY=stderr gh <command>. This will print the telemetry payload to your terminal instead of sending it silently, allowing you to see exactly what metadata is being packaged for GitHub’s servers.
How does this impact my professional Website Maintenance and support Services?
When you are providing Website Maintenance and support Services, you are often handling sensitive client environments. Telemetry adds an unvetted layer of communication between your local machine (or the client’s server) and a third-party corporation. Even if the data is just metadata, it can reveal work patterns, project activity levels, and environment configurations that some clients may consider a breach of their internal security or privacy policies.
Does disabling telemetry break any features of the CLI?
No. Disabling telemetry only stops the background reporting of usage statistics. The GitHub CLI will continue to function perfectly, and you will still have access to all the commands for managing pull requests, issues, and repositories.
Is setting an environment variable better than the config command?
Setting an environment variable (like GH_NO_TELEMETRY=1) is generally considered “safer” for privacy-conscious developers. While the gh config set telemetry off command works well, it only applies to that specific installation. An environment variable in your shell profile ensures that the setting persists even if you reinstall the CLI or move to a different machine.